The Administration's Clipper Chip Key Escrow Encryption Program: Hearing Before the Subcommittee on Technology and the Law of the Committee on the Judiciary, United States Senate (Classic Reprint): United States Committee on

Persuasion and Privacy in Cyberspace: The Online Protests over Lotus MarketPlace and the Clipper Chip: Gurak, Professor Laura J.: 9780300069631: Amazon.com: Books

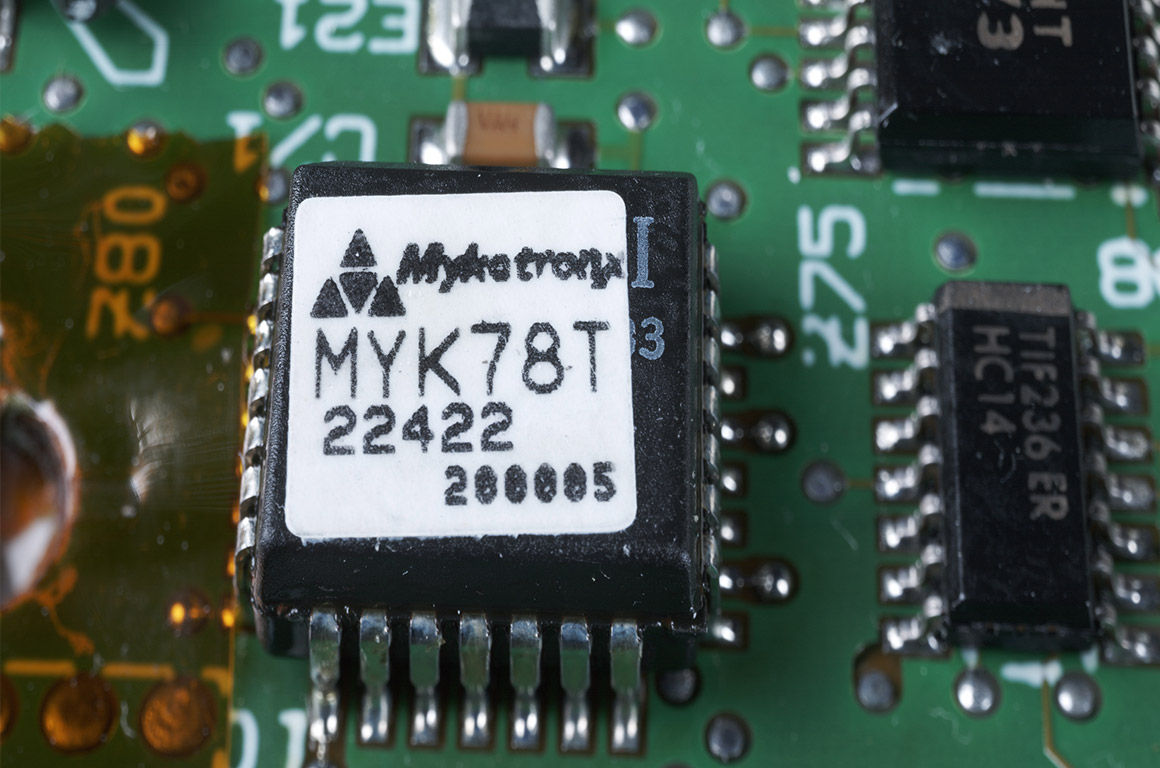
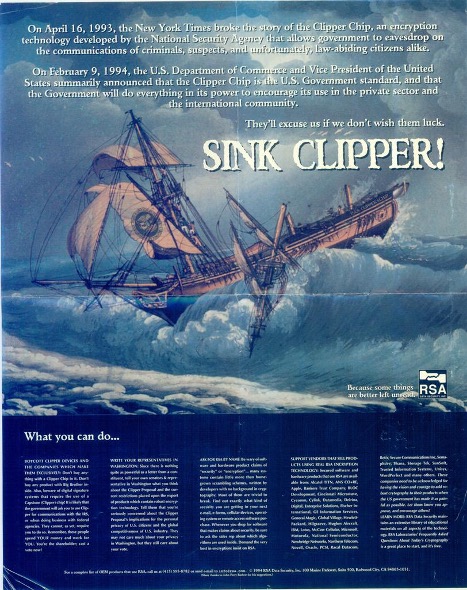
Remember the Clipper chip? NSA's botched backdoor-for-Feds from 1993 still influences today's encryption debates • The Register

U.S. Security Policy: The Dual-Use Regulation of Cryptography and its Effects on Surveillance | European Journal for Security Research

Representation of the communication of two clipper chips (own illustration) | Download Scientific Diagram