
The curriculum for the cybersecurity programs at Towson University,... | Download Scientific Diagram

2021 UIC Cyber Security Awareness Campaign: True Stories | Information Technology @ UIC | University of Illinois Chicago

Baylor Seeks to Educate, Raise Awareness of Data Privacy and Cyber Security | Media and Public Relations | Baylor University
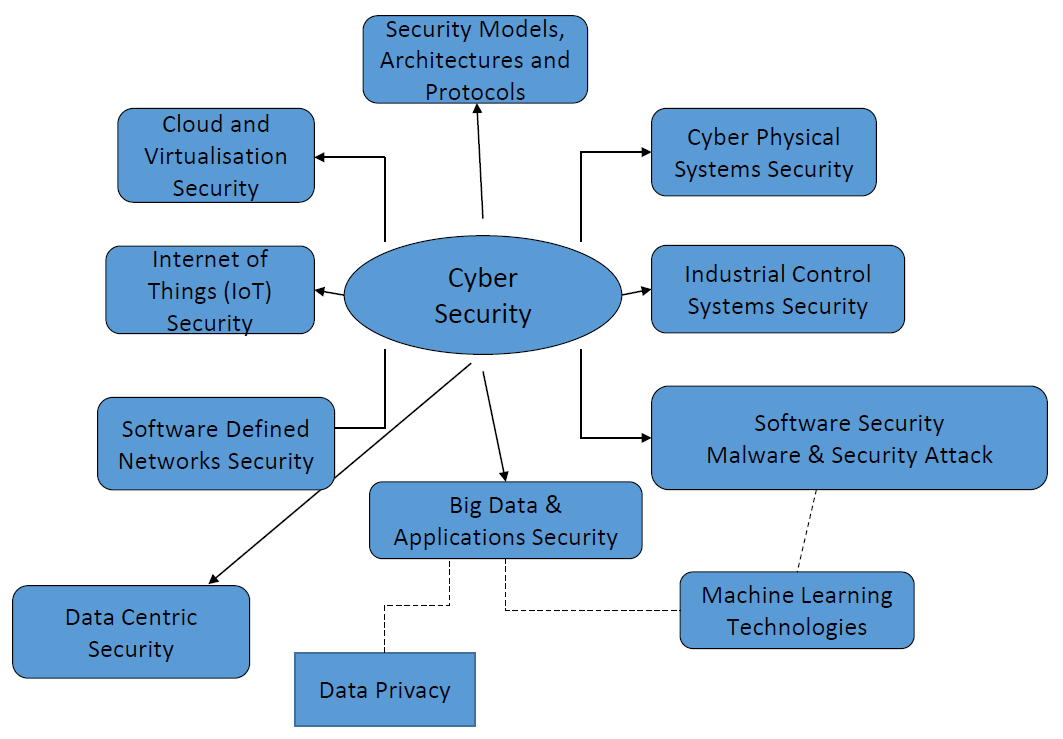
Research strategy / Research / Advanced Cyber Security Engineering Research Centre / Institutes and centres / Research / The University of Newcastle, Australia
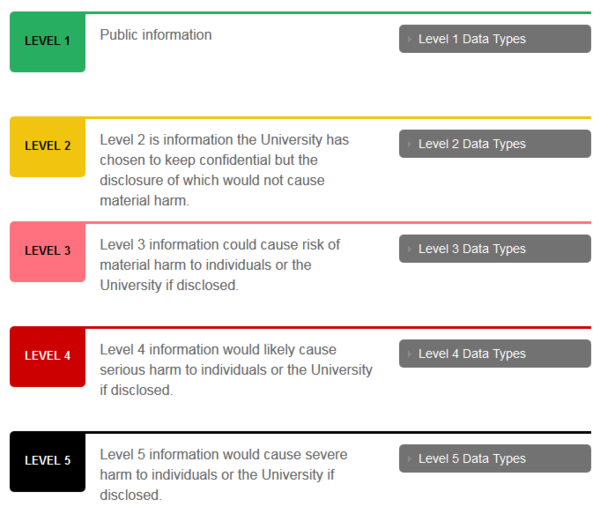
Information Security Policy Quick Reference Guide to Data Classification and Secure Data Handling - IT Help



![Best Data Security Courses & Certifications [2022] | Coursera Best Data Security Courses & Certifications [2022] | Coursera](https://d3njjcbhbojbot.cloudfront.net/api/utilities/v1/imageproxy/https://s3.amazonaws.com/coursera-course-photos/ab/93e9b701c64803b79ecc4ef287142c/Data-Security-Privacy_CourseraGraphics_1200x1200.jpg?auto=format%2Ccompress&dpr=1&w=330&h=330&fit=fill&q=25)













![Best Data Security Courses & Certifications [2022] | Coursera Best Data Security Courses & Certifications [2022] | Coursera](https://d3njjcbhbojbot.cloudfront.net/api/utilities/v1/imageproxy/https://s3.amazonaws.com/coursera-course-photos/c8/c284fb9e9f4324b2b2dc1866f5fb1e/Course-4-01.png?auto=format%2Ccompress&dpr=1&w=330&h=330&fit=fill&q=25)