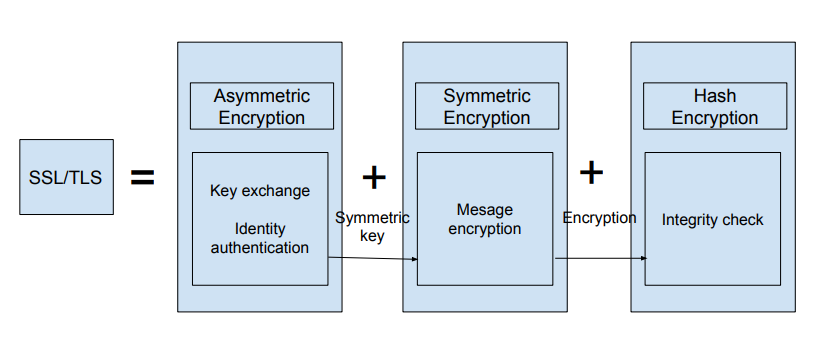
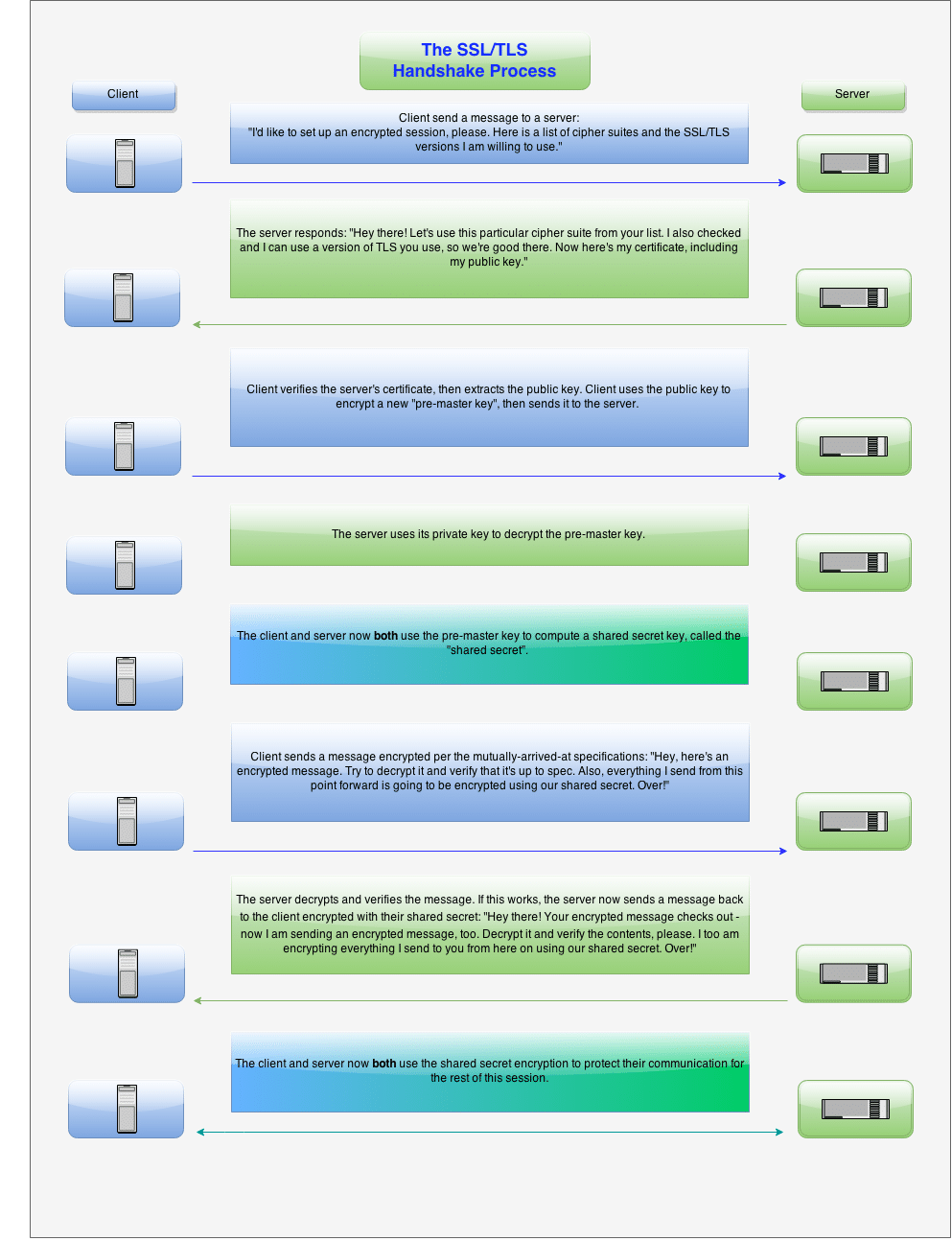
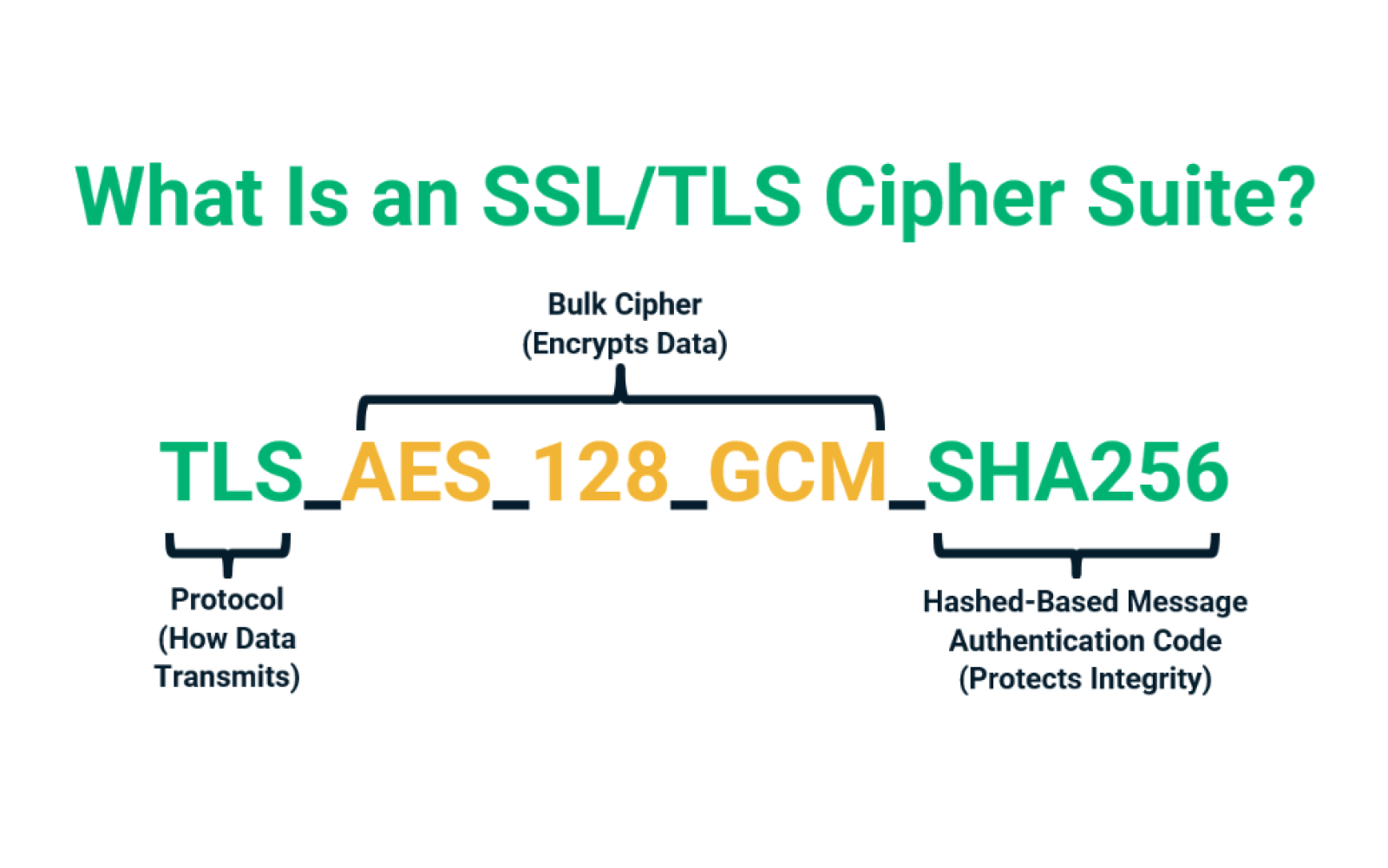
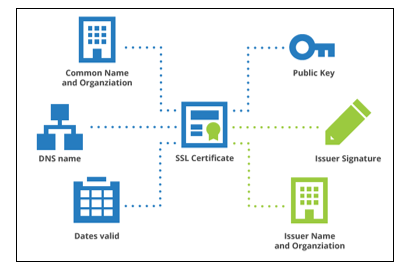
SSL/TLS — How does it work?. Encryption of data at rest as well as… | by Vikram Singh Jadon | Agile Software Development Company West Agile Labs

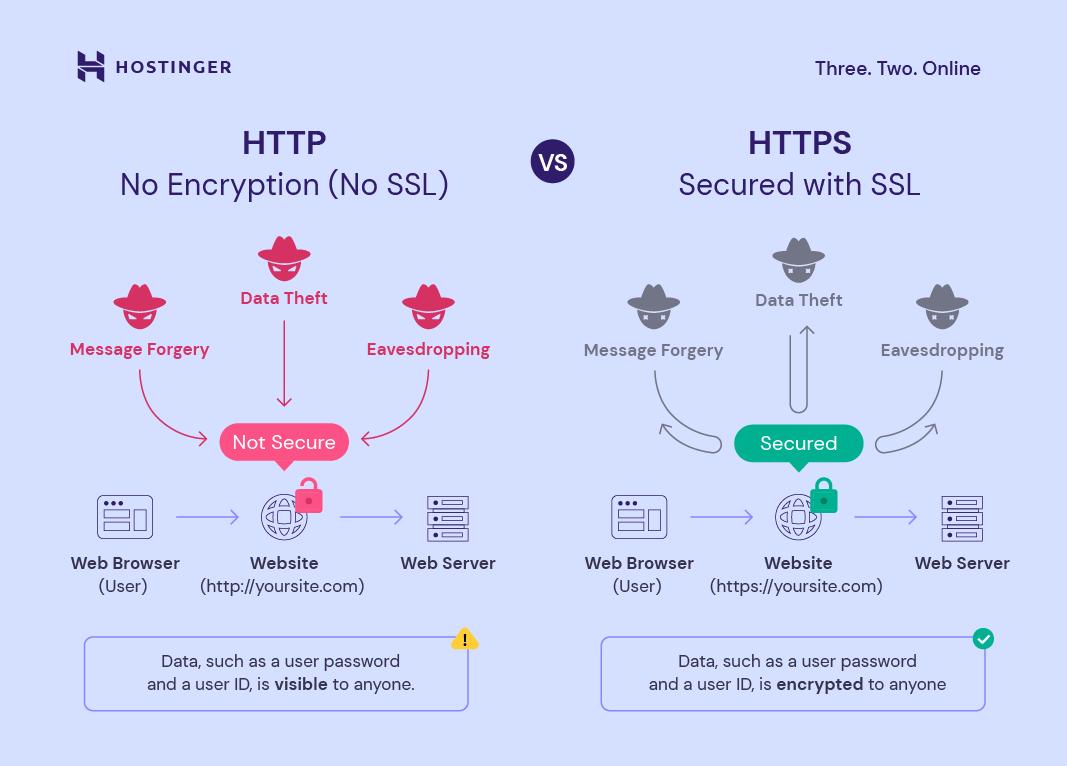
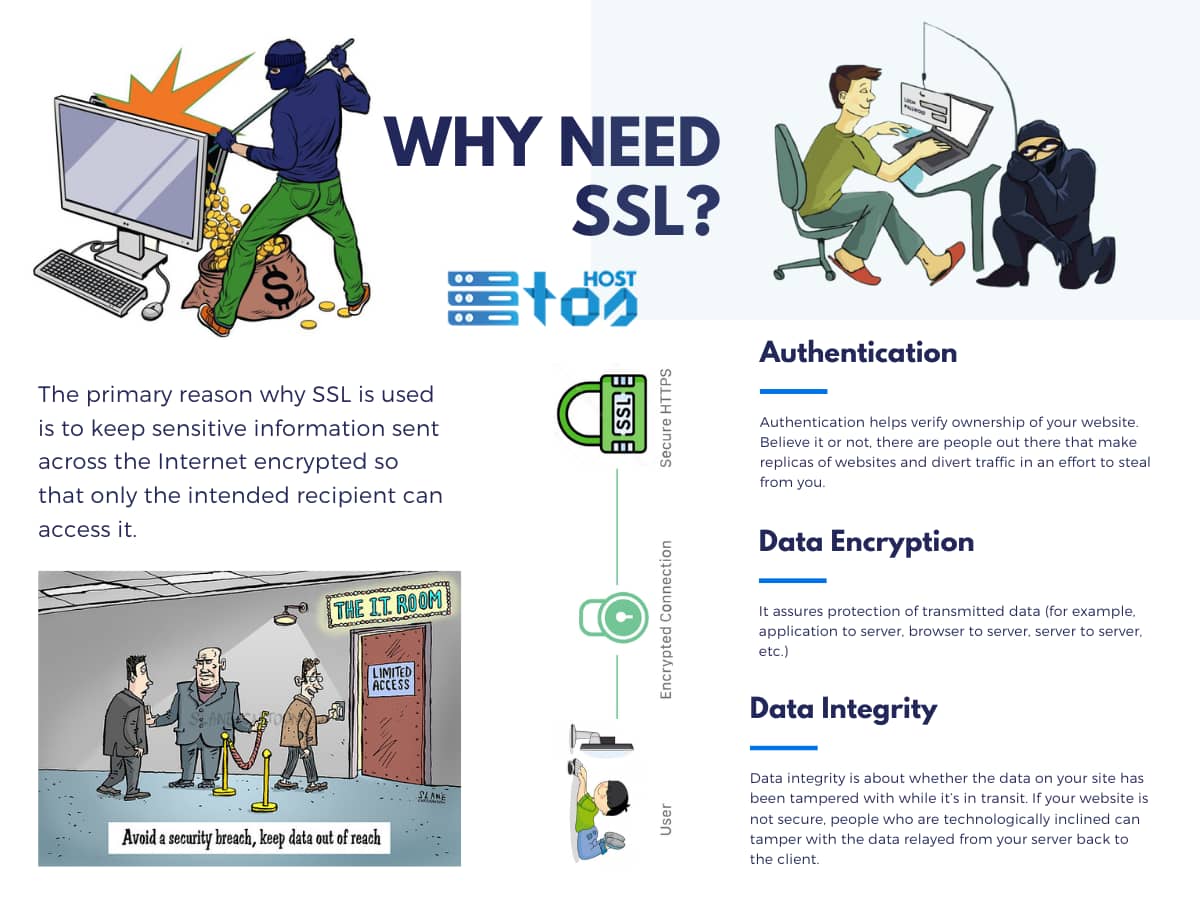
Protect your site with HTTPS / SSL, an Internet communication Protocol that protects data integrity and confidentiality .Secure web search flat isometric vector. Stock Vector | Adobe Stock

Addressing the OWASP Top 10 Application Security Risks with Web Application Isolation: #2 Cryptographic Storage and #8 Software and Data Integrity Failures - Zero Trust Edge

Addressing the OWASP Top 10 Application Security Risks with Web Application Isolation: #2 Cryptographic Storage and #8 Software and Data Integrity Failures - Ericom Blog

SSL Integrity (Which means you are receiving the same message as delivered by the sender) | Messages, The sender, Integrity

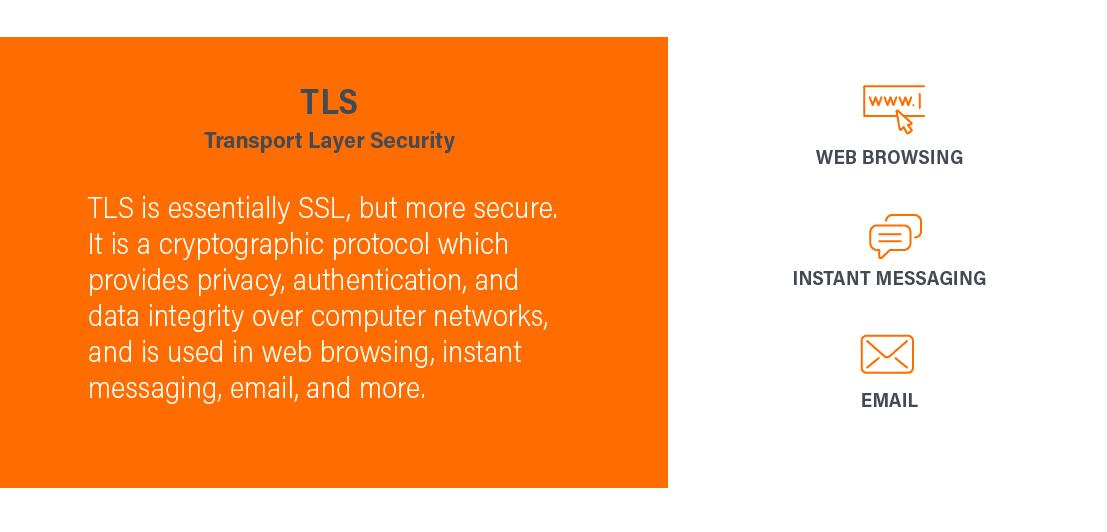
How do SSL & TLS protect your Data? - Confidentiality, Integrity, Authentication - Practical TLS - YouTube